English
Product & SolutionProduct & Solution

No signal? No problem.

The digital mirage: Who’s really online in the age of apps and AI?
Grow the pie, not your slice

The paradox of growth and exclusion

Reflections from MWC 2025

From 5G dreams to digital reality

Inclusive Innovation: How telcos can drive sustainable progress in a hyperconnected future

How Cloud Phone technology is driving Vietnam’s telco transformation

How Video Saved the World: Redefining Digital Inclusion through Video Content

Ushering in a New Era of Connectivity with Cloud Phone

Journey to the Cloud Phone: Revolutionizing Affordable Internet Access
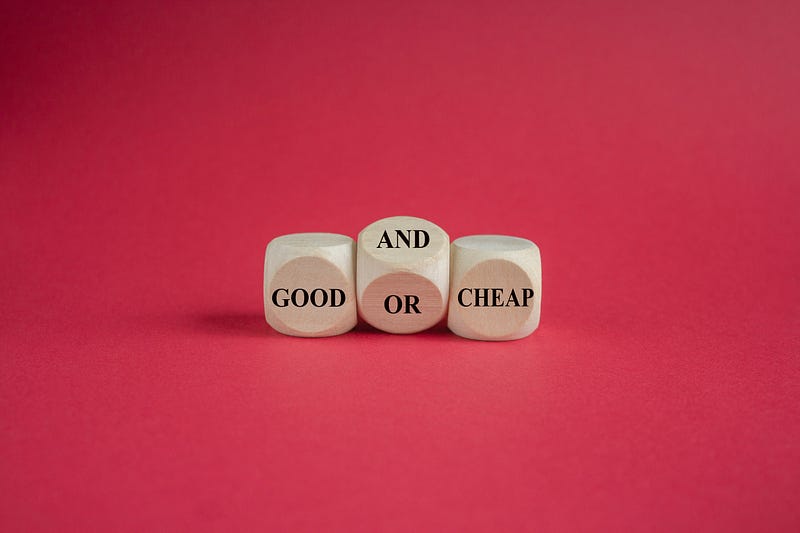
Cheap should not mean bad: why tech innovation and low price can coexist in harmony

Why connectivity also needs collaboration and cloud to crack digital inclusion

Cloud Phone redefines app development to empower the underserved

Technology can be a great equalizer as well as a divider

Five reasons why we can’t resist feature phones

The Cloud Phone experience

Cheap phones have never been this good

Why virtual Cloud Phone technology matters, and why it isn’t about you

Don’t let the sun set on your business growth

Bridging the B Gap

Making the feature phone smart (but not a smartphone)

Content providers need to cloud up or lose billions in the battle for user and subscriber growth

Cloud technology gives telcos a one-off chance to do something truly smart

Overcoming Obstacles: The Cloud Phone and the Path to Mobile Empowerment

Zero Trust and the Cloud Browser Solution

Rising Costs of Smartphones: Understanding the Factors, and Our Solutions
Hybrid Work

WFH Survival Kit: The Future of Work

WFH Survival Kit: Why You Should Start Planning Your Hybrid Work Strategy

WFH Survival Kit: Apps to Boost Your Work-From-Home Productivity

WFH Survival Kit: Setting Up a Work Environment At Home

WFH Survival Kit: Combating Stress and Burnouts

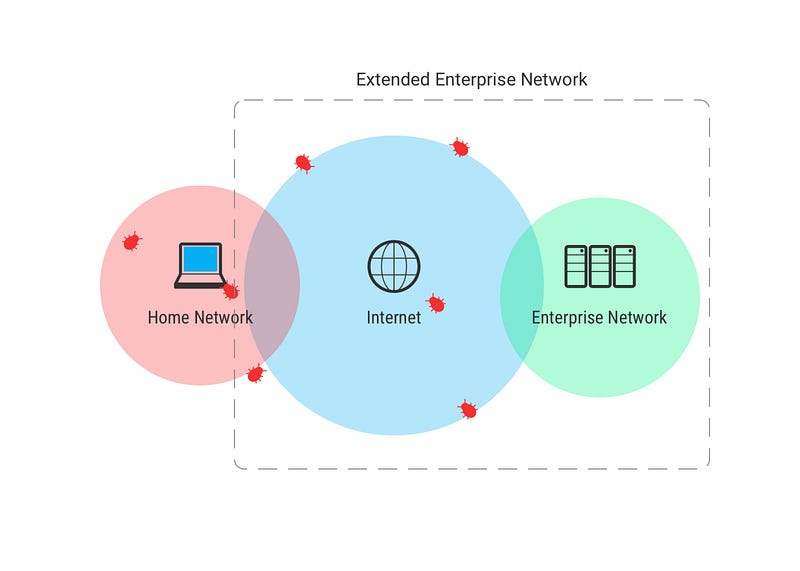
The New Frontier of WFH: Endpoint Security
Remote Browser Isolation and its Importance for WFH and Beyond
Security

Zero Trust and the Cloud Browser Solution
CloudMosa’s Cloud Avatar — the World’s Most Advanced Remote Browsing Platform

The Rising Threat of Cyberattacks in Taiwan: A Must-Read Report for Taiwanese SMEs and Industry…

CHSF Hospital Hack: What Happened, Our Analysis and Thoughts
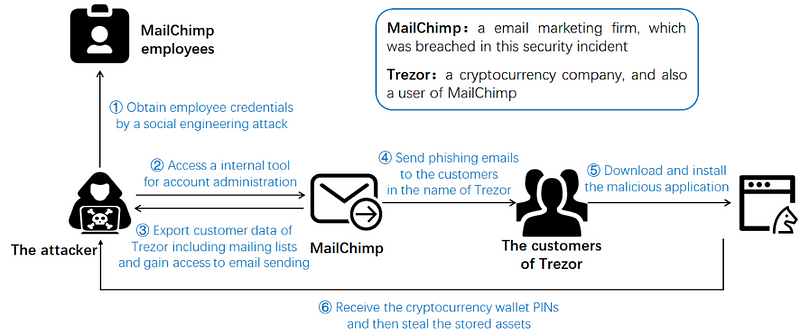
Cold wallet is not safe anymore. What can we do now?

Cloud Security: The Lifeline for Your Business, Today and Tomorrow. Part 2.

Cloud Security: The Lifeline for Your Business, Today and Tomorrow. Part 1.

WFH Survival Kit: Why You Should Start Planning Your Hybrid Work Strategy

Your Private Browsing Isn’t Really Private at All

The New Frontier of WFH: Endpoint Security
Remote Browser Isolation and its Importance for WFH and Beyond

The New Frontier of WFH: Rise of Corporate VPN and Security Threats
The New Frontier of WFH: Good Security Habits

True Privacy with Puffin Incognito
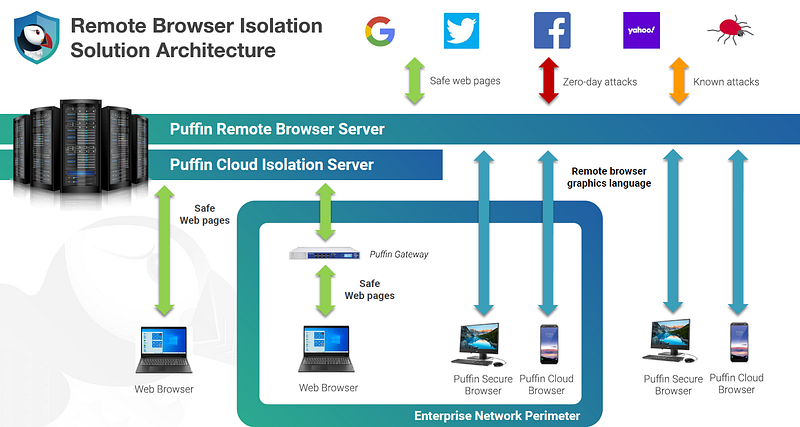
Puffin Secure Browser: A Browser that protect endpoints from current and future web threats

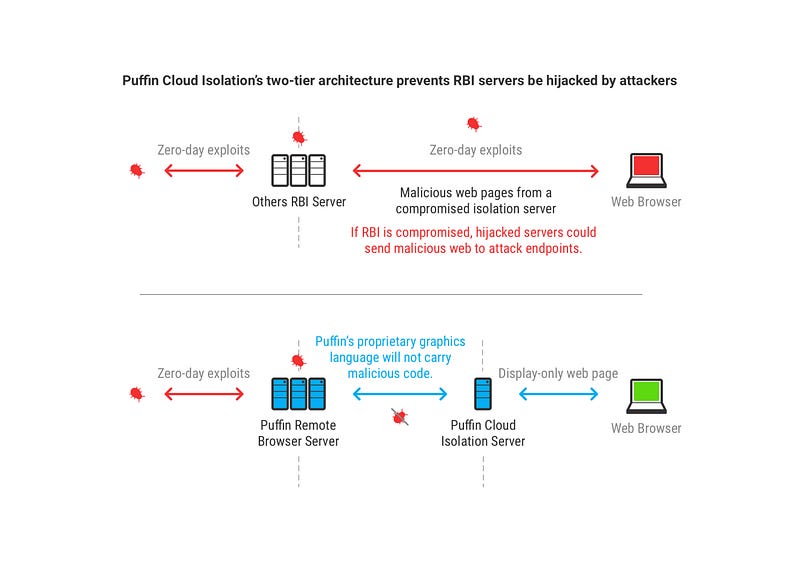
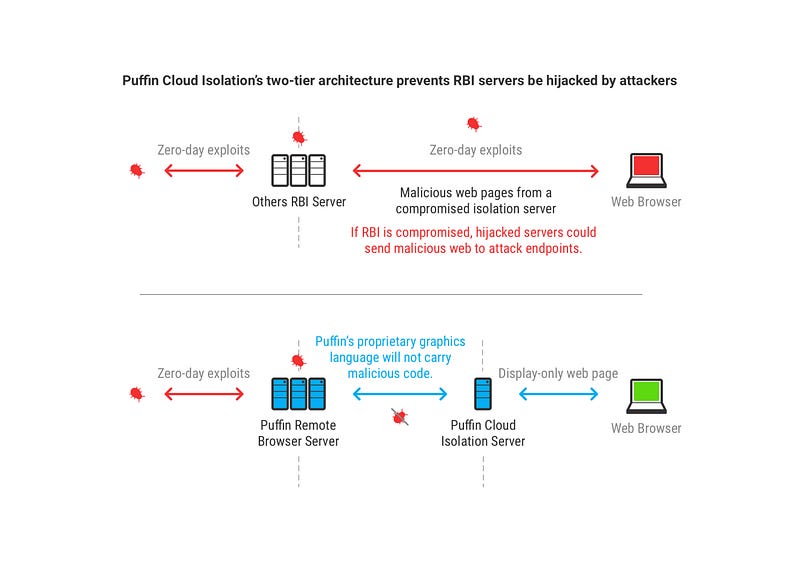
Future-proof Browser Security Against Zero-day:

Zero-day attacks: What it is, and how it works
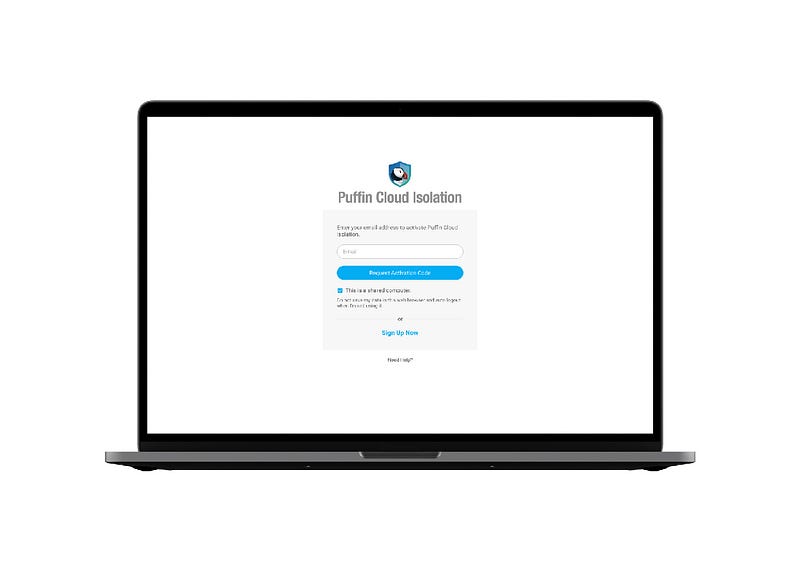
Puffin Cloud Isolation: Shared Computer Mode
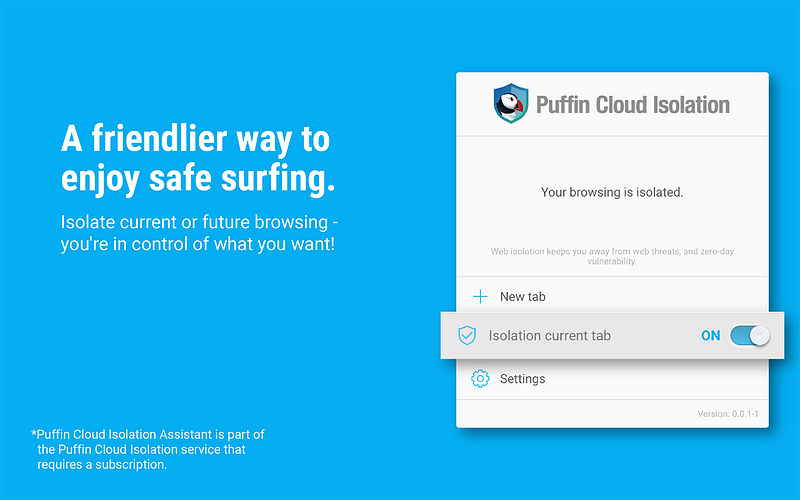
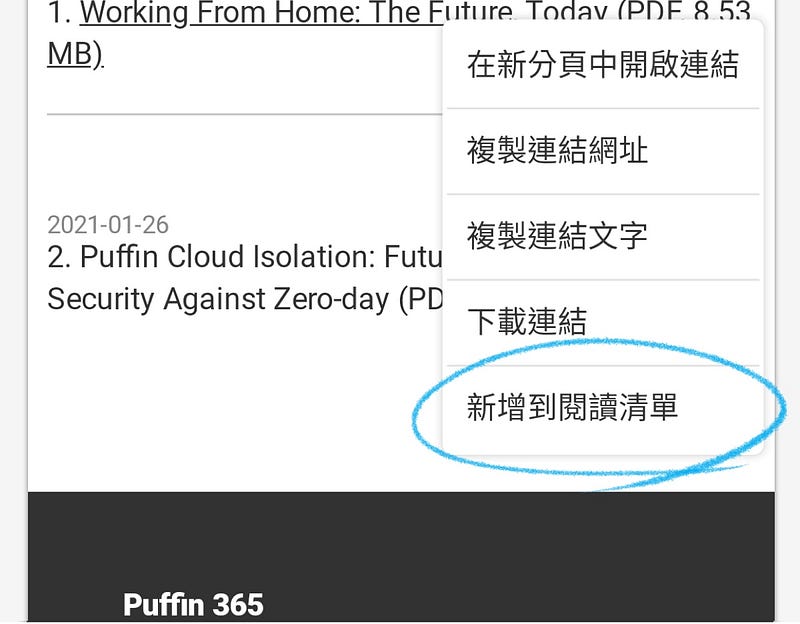
Puffin Cloud Isolation: Extension for your convenience

Puffin Cloud Isolation: Truly Valid Method of Web Isolation

Puffin Secure Browser is not hackable due to its extreme simplicityRemote Desktop is a good solution for secure web browser until remote desktop protocol is hacked. Puffin Secure Browser is probably the…
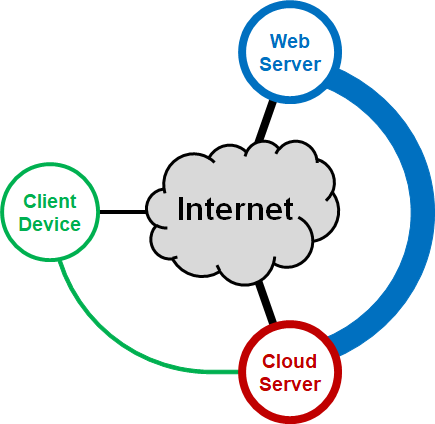
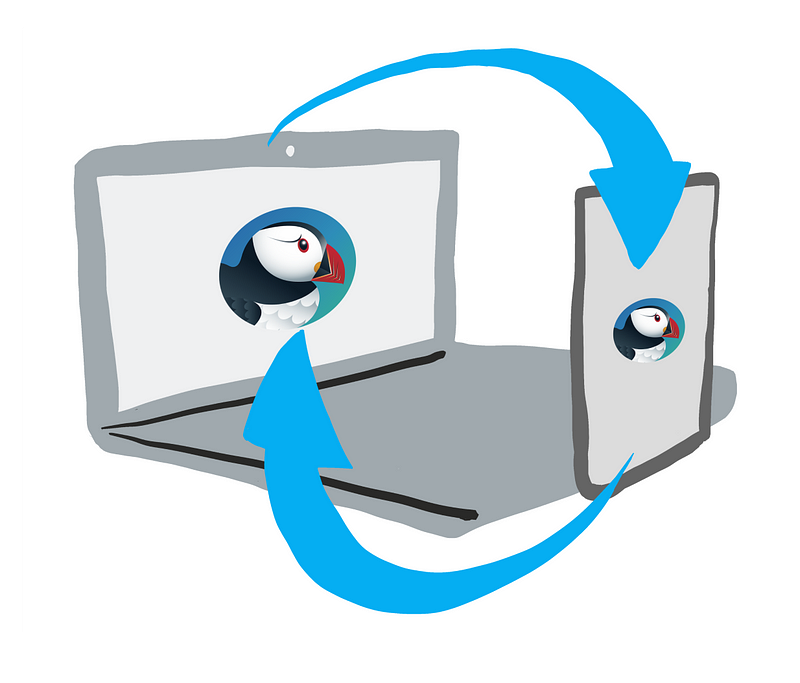
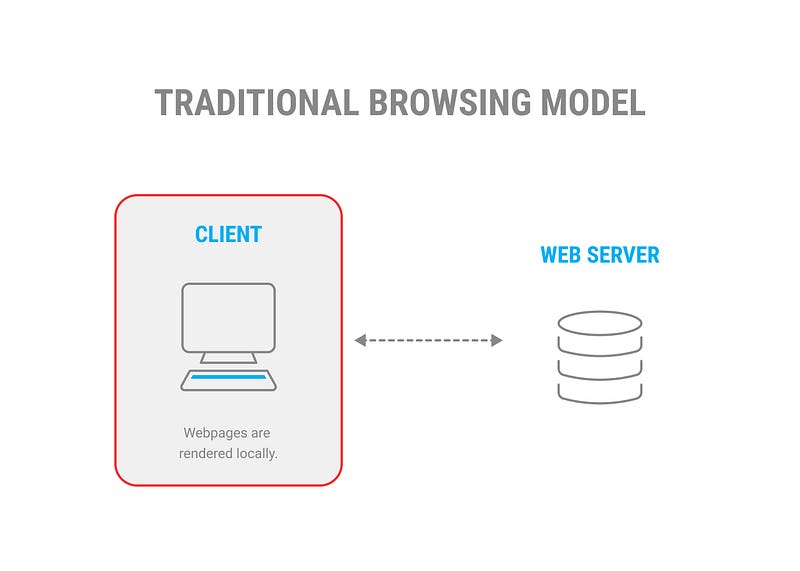
How Puffin Secure Browser works

Concerned about Online Security? Participate in Our Survey and Have Your Voice Heard!
Introducing Puffin Browser Lite, CloudMosa’s Newest Browser

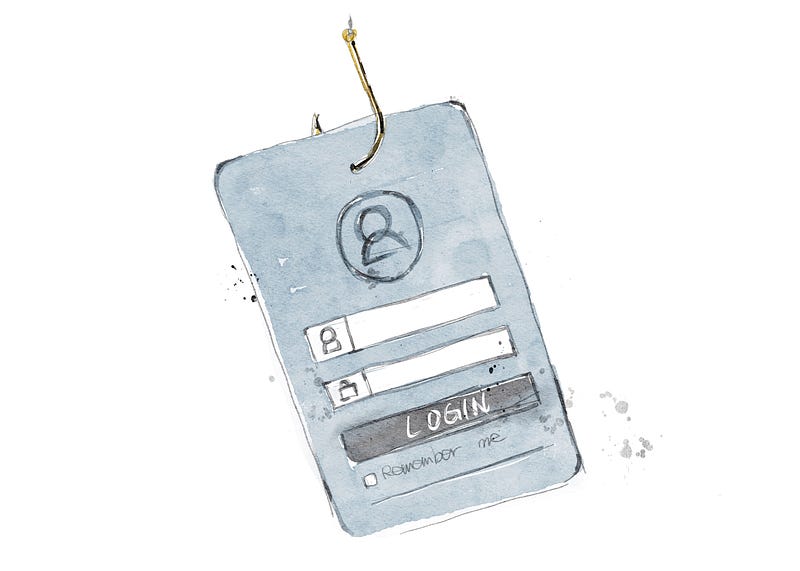
The Vulnerabilities of Digital Banking
Company News

A Letter to the People of Myanmar

What is the Difference Between Using a Computer and Using the Internet?We’ve previously scrutinized how much it actually costs to use the internet, but let’s also look into computer usage itself — specifically…

Another Milestone Achieved: CloudMosa Reaches 100 Million Users Worldwide

CloudMosa Celebrates 50 Million Global Users on Android Devices